Introduction
In an era defined by data breaches, pervasive surveillance, and rapidly evolving digital infrastructures, cryptography stands at the very heart of our collective security. Far more than arcane puzzles guarded by mathematicians, modern cryptography underpins everything from e-commerce to end-to-end messaging, from blockchain integrity to the safeguards of post-quantum networks. This sample blog post explores the journey of cryptography—from its ancient origins through its present-day applications—and peers forward to the breakthroughs that will shape our next wave of digital trust.
1. A Brief History of Secrecy
- Classical Ciphers: The Caesar and Vigenère ciphers introduced the concept of substitution and polyalphabetic schemes—simple yet effective methods that cloaked messages across battlefields and royal courts.
- World Wars & Mechanical Machines: The legendary Enigma and Lorenz machines showcased how electromechanical Rotors could automate complex substitutions, prompting the Allies to pioneer the first large-scale cryptanalysis efforts.
- From Theory to Practice: Claude Shannon’s mid-20th-century work laid the mathematical foundations of information theory and provable secrecy, transforming cryptography into a rigorous scientific discipline.
2. Cryptography Today—Beyond Passwords
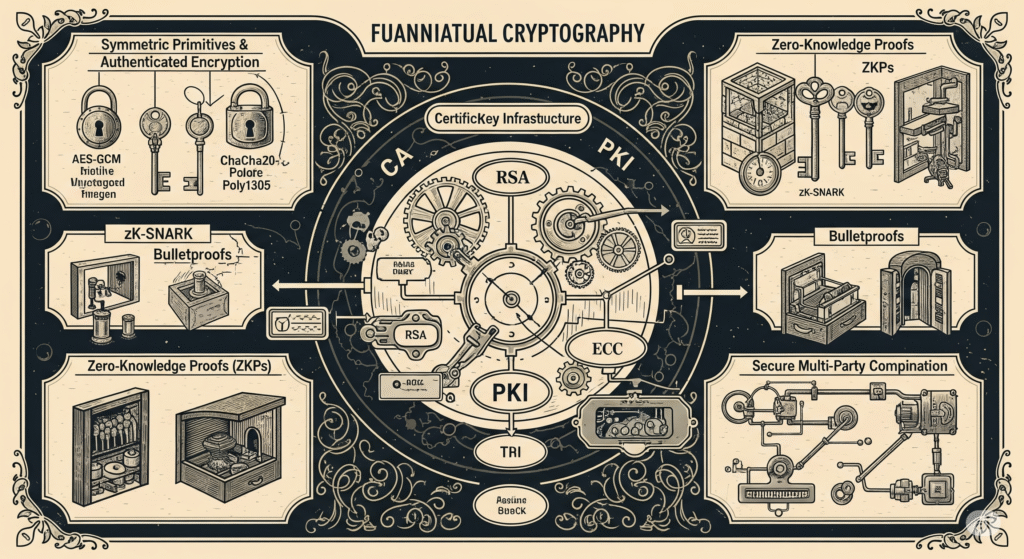
- Public-Key Infrastructures (PKI):
- Asymmetric algorithms like RSA, ECC, and their elliptic-curve counterparts enable secure key exchange over untrusted networks.
- Certificate Authorities (CAs) and Web PKI frameworks authenticate servers, devices, and users, underpinning HTTPS, code signing, and secure email (S/MIME).
- Symmetric Primitives & Authenticated Encryption:
- Advanced ciphers such as AES-GCM and ChaCha20-Poly1305 deliver both confidentiality and integrity with high performance, crucial for everything from SSD encryption to messaging apps.
- Zero-Knowledge Proofs (ZKPs):
- Cutting-edge ZKPs (e.g. zk-SNARKs, Bulletproofs) allow one party to prove knowledge of a secret statement without revealing the secret itself—enabling privacy-preserving blockchain transactions and anonymous identity attestations.
- Secure Multi-Party Computation (MPC):
- MPC protocols distribute computation across multiple participants, allowing joint computations on confidential inputs—promising revolutionary privacy in fields like collaborative machine learning and decentralized finance.
3. Real-World Applications
- End-to-End Encrypted Messaging: Signal, WhatsApp, and other platforms leverage the Double Ratchet algorithm to provide forward secrecy and post-compromise security.
- Blockchain & Distributed Ledgers: Hash functions, digital signatures, and consensus-driven key management underpin immutable transaction records and decentralized governance.
- Hardware Root of Trust: Secure Enclaves (Trusted Execution Environments) in modern processors isolate cryptographic operations from the host OS, bolstering device-level security for mobile, IoT, and cloud servers.
4. The Post-Quantum Challenge
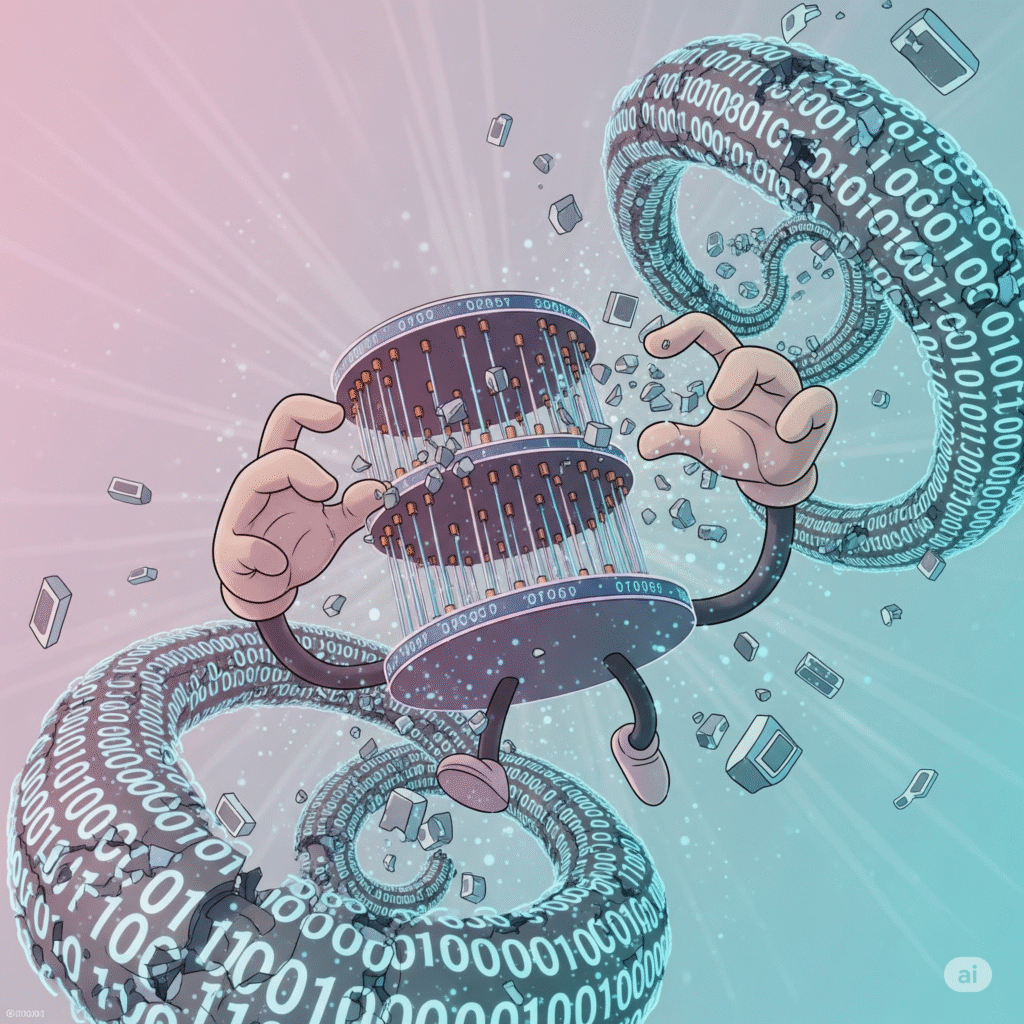
With the advent of quantum computers capable of subverting RSA and ECC, the cryptographic community is racing toward post-quantum algorithms:
- Lattice-Based Schemes (e.g. Kyber, Dilithium): Offer strong security reductions and practical performance.
- Code-Based & Multivariate Approaches: Provide alternative hardness assumptions, diversifying the cryptographic landscape.
NIST’s standardization effort means that organizations must plan for algorithm agility—designing systems that can smoothly transition to post-quantum ciphers once they are finalized.
5. Looking Forward—Innovation & Responsibility
- AI-Augmented Cryptanalysis: Machine-learning techniques are already aiding in side-channel attacks and differential cryptanalysis. Countermeasures must evolve in tandem.
- Decentralized Identity (DID): Self-sovereign identity frameworks, built on selective disclosure and verifiable credentials, will redefine how individuals control personal data.
- Sustainability in Cryptography: As blockchain networks and proof-of-work systems face scrutiny for energy use, greener consensus mechanisms (proof-of-stake, proof-of-history) and lightweight ciphers will become paramount.
Conclusion
Cryptography has always been a driving force behind secure communication, and its role will only expand as our world grows more interconnected. From safeguarding personal privacy to enabling the decentralized digital economy, the next decade will demand cryptographic frameworks that are resilient, scalable, and ethically designed. For practitioners and enthusiasts alike, the journey through this ever-evolving field remains as vital—and as exhilarating—as ever.
Leave a Reply